Trusted and Trustless Timestamping
An introduction (TL;DR)
Timestamping is a fundamental mechanism for establishing when digital data came into existence or was modified. It provides cryptographic proof of temporal precedence—demonstrating that specific information existed prior to a particular point in time. However, the way this proof is generated and verified differs dramatically depending on the trust model employed, giving rise to two distinct paradigms: trusted timestamping and trustless timestamping.
Trusted Timestamping
Trusted timestamping relies on a centralized or semi-centralized authority to manage and vouch for temporal records. In this model, a Time Stamping Authority (TSA) acts as a trusted third party that receives data, applies a cryptographic commitment (typically a cryptographic hash), and signs the resulting timestamp using PKI digital signatures. The standard governing this approach is RFC 3161, which defines how timestamps issued by a TSA should be structured and verified.
The security guarantee of trusted timestamping operates under a conditional assumption: provided that the timestamper's integrity is never compromised, no entity—not even the document owner—should be able to retroactively change or forge a timestamp once it has been recorded. The timestamp is typically encrypted using a PKI certificate, ensuring authenticity and preventing tampering.
Trustless Timestamping
Trustless timestamping addresses the fundamental limitation of trusted approaches: the requirement to trust an authority. This paradigm emerged with blockchain technology, which enables temporal records to be established through distributed consensus mechanisms rather than centralized institutions. In a trustless model, timestamps are embedded directly into an immutable, decentralized ledger accessible to all network participants.
Bitcoin and similar blockchains exemplify trustless timestamping by allowing anyone to record events and claim temporal precedence without relying on a third party. Projects like OpenTimestamps (OTS) formalize this capability by defining standardized methods for creating blockchain-based timestamps and independently verifying them. Rather than trusting a single entity, users rely on the cryptographic properties of the blockchain and the cost of rewriting history across a distributed network—making fraud computationally impractical.
Trustless timestamps take a little bit to complete, an initial "pending attestation" in a compact .ots proof file is released. This file can be later verified using opentimestamp.
Key Distinctions
The fundamental difference lies in where trust is placed. Trusted timestamping concentrates trust in institutional entities and their security practices, while trustless timestamping distributes trust across cryptographic mathematics and decentralized consensus. Each model has practical implications: trusted approaches provide regulatory compatibility and institutional accountability; trustless approaches offer resilience against institutional compromise but require users to understand blockchain mechanics and pay transaction fees (though services like OTS aggregate requests to reduce costs).
Trusted timestamps are recognized at an European level due to eIDAS regulation; whereas trustless timestamps are recognized also in Italy (and other few member states).
Web Trust Timestamps
In Web Trust, timestamps can be generated using API calls or directly using the web interface.
The web interface allows you to upload a file to be timestamped, select whether to using trusted or trustless timestamping, wait some seconds and the timestamped file will be downloaded automatically to the download location configured in your browser.
The following image shows the web interface:
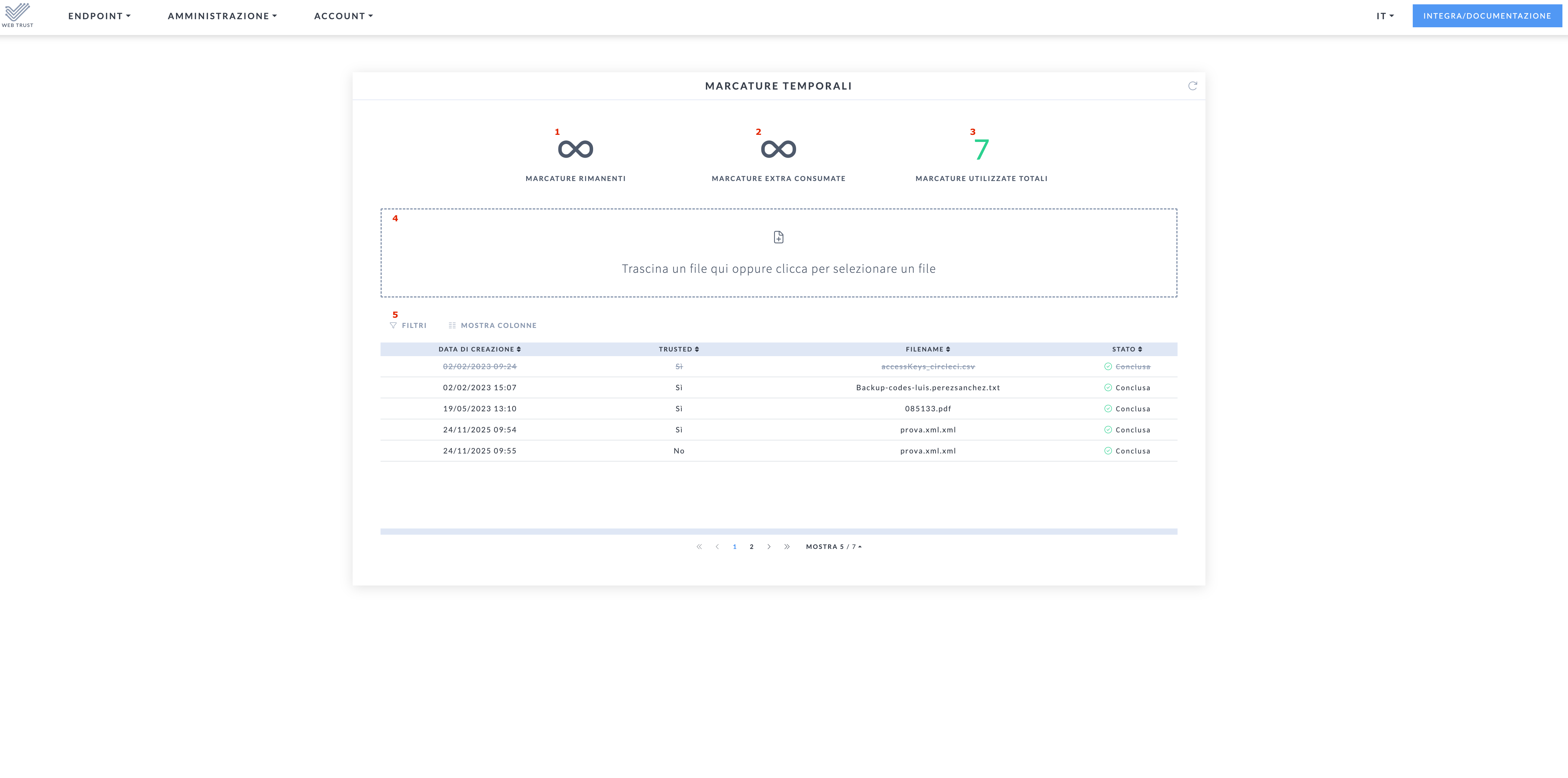
Where:
is the remaining pre-paid timestamps in the current billing period
is the amount of over-quota (timestamps consumed beyond the pre-paid ones) in the current billing period
is the total of consumed timestamps
is the area where you can drop a file to be timestamped. One the file is drop you will be presented with the following choice:
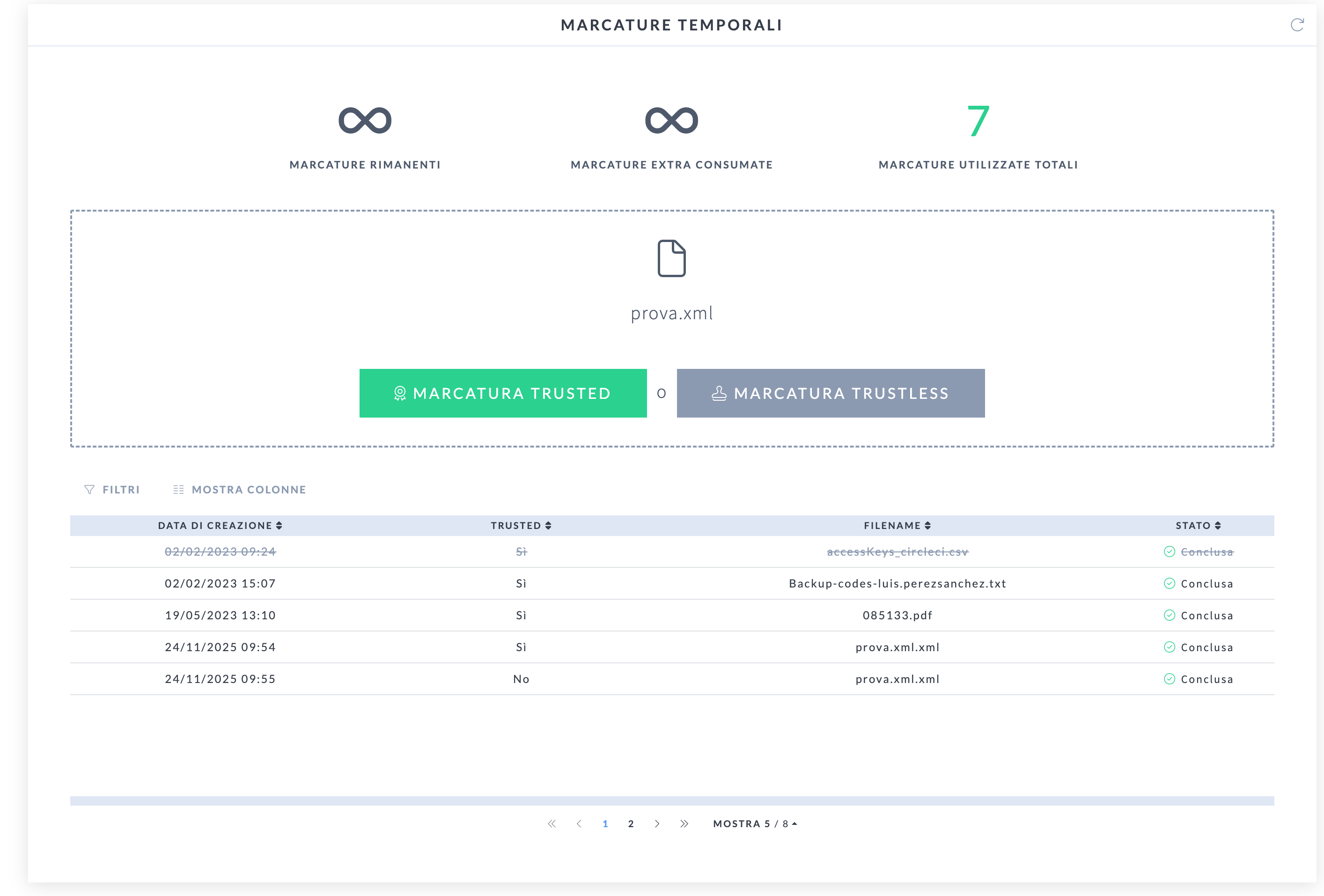
Once you select the type of timestamp you want to apply, the file will be automatically:
uploaded
timestamped
downloaded
is a table containing all timestamps you have done, it is just a log, the timestamps are not preserved in our systems.
File extensions
Web trust supports the timestamp of any kind of file, there is just a technical limitation regarding the file dimension; it must be less than 20MB.
Trusted
Once a file is timestamped using a trusted timestamp, Web Trust will produce a file with exactly the same name and extension of the uploaded file, but adding the .tsd extension.
A TSD file is self contained, meaning that it has the original file plus the timestamp inside.
To check a TSD file avoid opening it yourself locally, use a third-party service like this one.
Trustless
For this type of timestamp, an OTS file will be downloaded. This means that the extension .ots will be added to the original file name.
An OTS it is not self contained, so the original file must be preserved together the .ots corresponding file.
In order to verify an OTS file you can use opentimestamps. Remember that you will need to preserve the original timestamped file.